Hidden crypto mining viruses hijack your computer’s CPU to mine cryptocurrency without your knowledge, causing slowdowns and high resource usage. Traders face high risk when launching trading apps or browsers from untrusted sources.
Modern trading relies on computers, where turning on machines, trading terminals, and browsers exposes you to hidden miners.

Contents
- Hidden Crypto Mining: What It Looks Like
- How to Detect and Remove Hidden Mining Viruses
- How Miner Viruses Disguise Themselves and How to Fight Them
- Conclusion
Hidden Crypto Mining: What It Looks Like
For traders’ PCs, the main operating systems are Windows, Linux, and OS X. Linux and OS X have architectures that reduce virus risks, and fewer users make them less targeted.
Windows powers 9 out of 10 traders, making it a prime target for malware like hidden miners from spam emails or unknown files.
How to Detect and Remove Hidden Mining Viruses
The simplest viruses max out your PC’s resources for mining, causing dramatic slowdowns.
Open Task Manager to spot the process eating most resources—that’s likely the miner. It often masquerades as opera.exe or skype.exe.
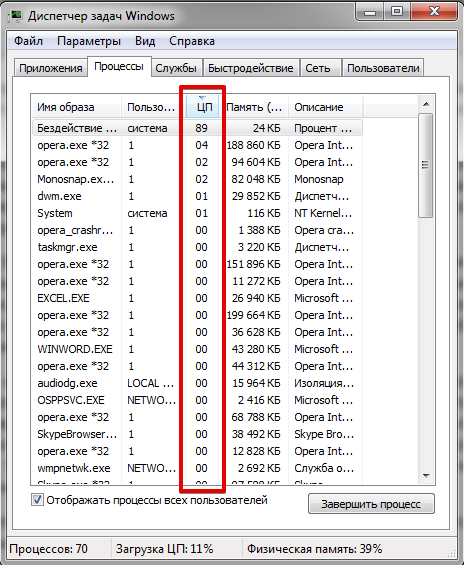 How a hidden mining virus appears in Windows Task Manager
How a hidden mining virus appears in Windows Task Manager
Right-click the process, select “Open file location”—if it’s not in the original folder, it’s fake.
If the process is a disguised mining virus, its file will not be located in the original folder.
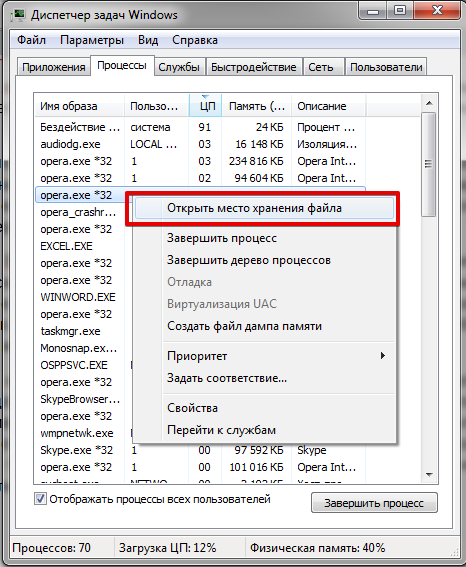 How to detect a hidden mining virus on a PC
How to detect a hidden mining virus on a PC
Check user rights too—system processes don’t run under regular user accounts. End the process, run antivirus, and trace the source.
How Miner Viruses Disguise Themselves and How to Fight Them
Miner authors use disguises to avoid detection from slowdowns. Here are the three most common methods.
Method 1: Virus Disguised as a System Service
These hide in svchost.exe, a legit process you can’t kill without crashing Windows.
What to do? Use msconfig.exe or better, free Process Explorer to link services to resource hogs and research them.
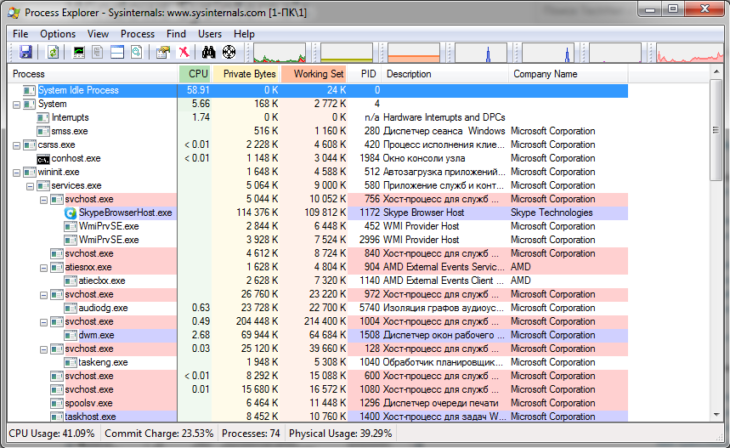 Process Explorer to catch hidden mining viruses
Process Explorer to catch hidden mining viruses
Method 2: The Non-Greedy Miner
These use resources sparingly, pause during heavy apps, and monitor fans to stay hidden.
What to do? Check Task Manager, but use Process Explorer, Everest, or AIDA64 for desktop monitoring widgets.
Method 3: Advanced Level Disguise
Miners use rootkits with admin rights to hide from Task Manager and antivirus.
A rootkit hides viruses by altering system functions, like excluding its process from lists.
What to do? Monitor network activity on your router—idle PCs don’t connect constantly to mining pools. Seek pros if found.
Conclusion
Stay vigilant: avoid untrusted downloads. Sudden slowdowns or odd activity signal possible hidden mining on your trading PC.
FAQ
What causes sudden PC slowdowns during trading?
Hidden miners max out CPU for crypto like Monero, disguised as system processes.
How do I confirm a suspicious process is a miner?
Right-click in Task Manager, check file location and user rights—if mismatched, it’s likely malware.
What’s the best free tool to detect advanced miners?
Process Explorer reveals hidden services and resource links; pair with antivirus for removal.