Cryptocurrency mining has gained tremendous popularity today. There are countless videos online explaining how to mine cryptocurrencies at home. However, in this article, we offer a different perspective on the cryptocurrency mining process.
Modern trading is impossible without computers. Every trader starts their workday by turning on their machine, launching trading terminals, necessary applications, and browser tabs. It is precisely at these moments that they risk becoming victims of hidden mining.

Contents
- Hidden Cryptocurrency Mining: What It Looks Like
- How to Detect and Remove Hidden Mining Viruses
- How Miner Viruses Disguise Themselves and How to Fight Them
- Conclusion
Hidden Cryptocurrency Mining: What It Looks Like
For personal computers used by almost all traders, there are currently three most common operating systems: Windows, Linux, and OS X.
The latter two have unique architectures that significantly reduce the chance of catching a virus. Moreover, the number of Linux and OS X users is relatively small, so creating viruses for these systems is uncommon and sporadic.
Windows, however, is used by 9 out of 10 traders. Writing various malware for Windows is widespread—just recall the spam emails about million-dollar inheritances landing in your spam folder. Running any unfamiliar file on your machine carries potential risks and may install a hidden mining virus.
How to Detect and Remove Hidden Mining Viruses
The simplest viruses fully utilize your PC’s resources for mining. As a result, your computer starts to slow down dramatically.
Detecting such a basic mining virus is quite straightforward, explains the technical team at Forttraders magazine. You need to open the Task Manager and check which process is consuming the most system resources. That process is likely the virus mining cryptocurrency on your PC for attackers.
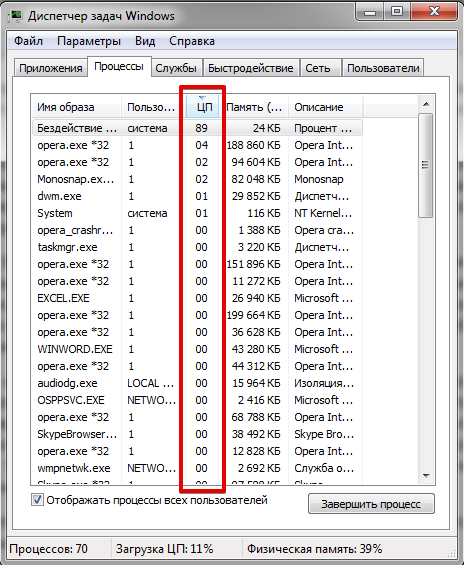 How a hidden mining virus appears in Windows Task Manager
How a hidden mining virus appears in Windows Task Manager
Of course, such a virus is unlikely to be named cryptominer. Most likely, it will be disguised as a system process or a well-known program, such as opera.exe, skype.exe, etc.
To verify the disguise, check the file location by right-clicking the process and selecting “Open file location.”
If the process is a disguised mining virus, its file will not be located in the original folder.
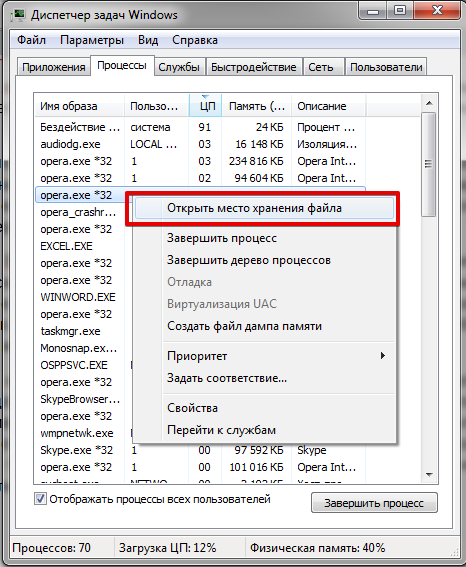 How to detect a hidden mining virus on a PC
How to detect a hidden mining virus on a PC
Another sign of a hidden cryptocurrency miner is the user rights under which it runs. As you know, a system process cannot run with regular user rights.
If you have fallen victim to hidden mining in this form, the cure is simple. You need to end the process, clean your computer with an effective antivirus, and most importantly, recall where you might have caught this miner and learn from the experience.
How Miner Viruses Disguise Themselves and How to Fight Them
Even novice users know that if a computer slows down, it probably has a virus and needs cleaning. For this reason, mining virus authors use various disguise methods. Here are the three most common ones.
Method 1: Virus Disguised as a System Service
If a mining virus disguises itself as a service, you won’t see a separate process in Task Manager. Instead, system resources will be used by a process like svchost.exe, which is a legitimate system process. Ending it will likely cause your Windows to freeze.
What to do in this situation? You can search for suspicious services via msconfig.exe, but a much more effective way to detect hidden miners is using the free program Process Explorer.
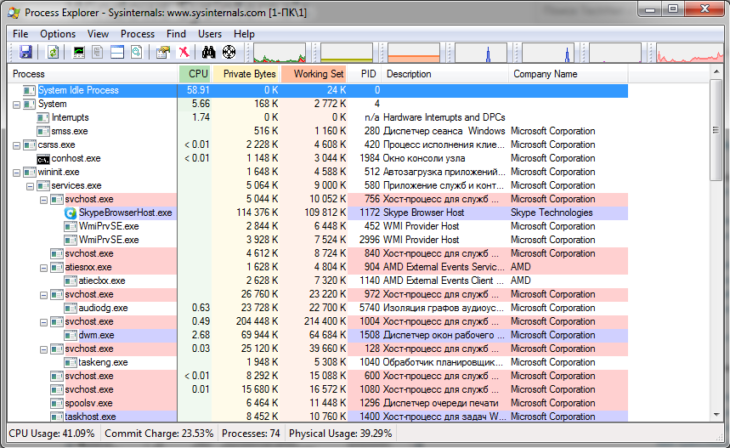 Process Explorer to catch hidden mining viruses
Process Explorer to catch hidden mining viruses
With this program, find the most resource-intensive process and the services linked to it. Then, using search engines, find information about each service to identify the hidden mining virus.
Method 2: The Non-Greedy Miner
The second method focuses not on rapid cryptocurrency mining but on maximizing the virus’s lifespan. Such a miner uses system resources moderately and pauses its activity when resource-heavy programs run, so as not to slow down the OS and avoid detection.
Advanced mining viruses even monitor fan speed to avoid revealing themselves during system idle times by excessive CPU usage.
What to do in this situation? Again, you can look for suspicious processes in Task Manager. However, some miners completely stop working when launched, making detection this way unlikely.
The most effective approach is to use third-party tools like Process Explorer. Free programs like Everest or AIDA64 are also useful, as they allow you to place system load monitoring widgets on your desktop.
Method 3: Advanced Level Disguise
The third and most dangerous disguise method is the use of rootkits by miners.
For those unfamiliar, a rootkit is a set of software tools that hide a virus by gaining Administrator rights on your computer.
All programs on a computer use certain system functions. For example, a miner-rootkit can replace the “Show all processes” function with “Show all processes except cryptominer.exe.” As a result, neither Task Manager nor even the most effective antivirus can detect such a virus miner.
What to do in this situation? The revealing sign of a miner-rootkit is its network activity. Monitoring this activity must be done directly on the router or a specially configured proxy server on another machine.
The idea is that a rootkit miner must maintain constant communication with the mining pool. A regular computer, if left idle, hardly accesses the Internet. This contrast reveals the presence of a hidden mining virus in your system. If you detect such activity, it is unlikely you can handle it yourself—you will need professional help.
Conclusion
No one is immune to mistakes, but being informed means being prepared. Remember not to download everything indiscriminately from the Internet. If your computer suddenly slows down drastically or you notice suspicious activity, it’s a sign to consider whether someone might be secretly mining cryptocurrency using your PC.










